News

After A Major Hack, U.S. Looks To Fix A Cyber ‘Blind Spot’
By: Greg Myre | NPR
Posted on:
WASHINGTON, D.C. (NPR) — The National Security Agency considers itself the world’s most formidable cyber power, with an army of computer warriors who constantly scan the wired world. Yet by law, the NSA only collects intelligence abroad, and not inside the U.S.
U.S. rivals like Russia are aware of this blind spot and know how to exploit it, as the NSA director, Army Gen. Paul Nakasone, explained recently to the Senate Armed Services Committee.
“We may see what’s occurring outside of the United States, but when it comes into the United States, our adversaries are moving very quickly,” Nakasone testified on March 25. “They understand the laws and the policies that we have within our nation, and so they’re utilizing our own infrastructure, our own Internet service providers, to create these intrusions.”
In a major breach last year, hackers widely believed to be from Russia’s foreign intelligence service, the SVR, placed malware on a software update produced by the Texas company Solar Winds.
No one had reason to be suspicious, or the legal authority to monitor, as that software update was sent out electronically from SolarWinds to 18,000 organizations, including nine U.S. government agencies.
“It’s not the fact that we can’t connect the dots. We can’t see all of the dots,” Nakasone said.
Privacy protections
The U.S. Constitution’s Fourth Amendment bars the government from domestic surveillance unless a crime is suspected.
But in the digital age, these U.S. privacy protections have an unintended consequence. They help hide foreign intelligence agencies that can disguise their tracks and make it appear as if they are operating from inside the U.S.
This is fueling a debate on how the U.S. government and private tech companies can protect both computer networks and civil liberties.
None of the leading figures in this debate are suggesting that privacy laws protecting Americans should be rolled back. But they are saying the U.S. must find a better way to guard against foreign spy agencies.
SolarWinds was just one of several U.S. companies that the hackers tapped into to cover their tracks, said Glenn Gerstell, who was the NSA’s general counsel until he stepped down last year.
“The Russians rented a computer server capability on a network hosting company, GoDaddy,” said Gerstell. “Just like I can go buy a website on GoDaddy, so too can the Russians.”
Of course, the hackers used multiple layers of deception to hide their identity and make it look as if they were Americans, Gerstell said. This meant that even if U.S. cybersecurity teams suspected something was amiss, the bread crumbs weren’t leading back to Russia.
“Someone looking at their computer in the United States, to see whether it was doing anything funny, would see communications from their computer to another computer in the United States on GoDaddy, which doesn’t look particularly suspicious,” he said.
Extensive hacking
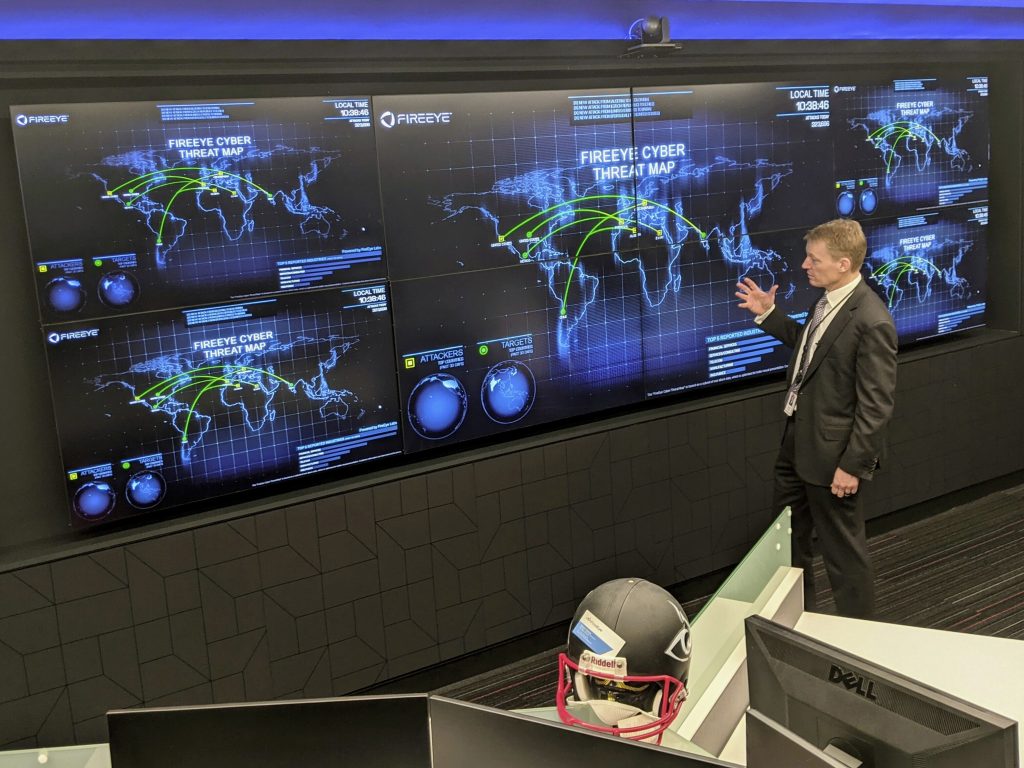
The hackers rummaged through computer networks belonging to the U.S. government agencies and dozens of private companies starting in March 2020. They weren’t detected until December 2020 — by yet another U.S. company hit in the attack — the California cybersecurity firm FireEye.
FireEye is one of the country’s leading cybersecurity firm. It’s the company the U.S. government and large corporations call when they fear they’ve been hacked.
“We recognized right away that FireEye was one of many victims, ” the company’s CEO, Kevin Mandia, said at a recent conference held by The Cipher Brief.
Mandia, a former Air Force computer security officer, says the U.S. government needs a central location where the government and the private sector can deal with suspected hacks in real time.
“Regardless of the agency chartered with doing it, you will have to have a clearinghouse for intel that’s a single point. You just do. I don’t care what you call it, but it’s got to be private and public-sector thing,” he said.
The present system is far too slow and cumbersome, according to Mandia and others.
If the NSA detects unusual computer traffic coming from abroad, it is not allowed to track it inside the U.S. The agency can notify the FBI, which can then seek court permission and consult with the U.S. company that may be the target. While all this plays out, likely over the course of days, a skilled hacker may have already come and gone.
If a private U.S. company detects an intrusion, as happened with FireEye in December, it’s not legally required to share that information with the government or anyone else. Many companies are reluctant to report a hack, fearing the disclosure will harm their reputation and stock price.
FireEye’s willingness to publicly acknowledge that it was breached, and to work with the government and other private companies, has been praised for helping limit the damage.
Neither the government nor the companies targeted have disclosed the full extent of the damage.
New proposals
Meanwhile, Gerstell, the former NSA general counsel, is working on his own proposal.
“What we can do is create some kind of fusion center,” he said. “The FBI, together with the NSA and CISA from Homeland Security, can all pool together their resources, their computers, and work together in real time with the private sector.”
CISA, the Cybersecurity and Infrastructure Security Agency, was just established in 2018 to deal with domestic cybersecurity issues. The agency played a leading role in safeguarding U.S. elections last year. But as a relatively new and small agency with limited authority, cybersecurity experts say CISA is not yet equipped to play the role that’s needed.
However, Sen. Ron Wyden, an Oregon Democrat, is a skeptical when he hears about plans to expand the government’s cybersecurity reach.
“The impression the American people might get is that the hackers are such formidable adversaries that there was nothing that the American government or our biggest tech companies could have done to protect themselves,” Wyden said at a recent hearing of the Senate Intelligence Committee on the SolarWinds hack.
“My view is that message leads to privacy-violating laws and billions of more taxpayer funds for cybersecurity,” he added. “There are concrete ways for the government to improve its ability to identify hackers without resorting to warrantless monitoring of the domestic Internet.”
The White House says President Biden will respond soon to the SolarWinds hack, but has not provided details.
The Biden administration also says it’s working on ways for the government and the tech industry to better share critical information. But the administration stresses that it’s not currently seeking increased legal authority for domestic digital surveillance.
Greg Myre is NPR national security correspondent. Follow him @gregmyre1.
9(MDI4ODU1ODA1MDE0ODA3MTMyMDY2MTJiNQ000))

